-
Notifications
You must be signed in to change notification settings - Fork 67
Home
shusei tomonaga edited this page Jul 2, 2019
·
6 revisions
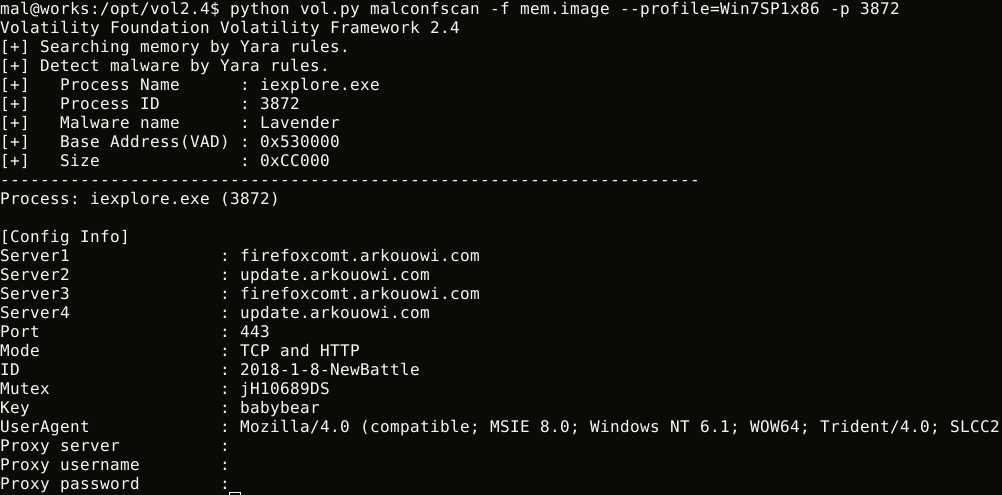
MalConfScan is a Volatility plugin extracts configuration data of known malware. Volatility is an open-source memory forensics framework for incident response and malware analysis. This tool searches for malware in memory images and dumps configuration data. In addition, this tool has a function to list strings to which malicious code refers.
MalConfScan can dump the following malware configuration data, decoded strings or DGA domains:
- Ursnif
- Emotet
- Smoke Loader
- PoisonIvy
- CobaltStrike
- NetWire
- PlugX
- RedLeaves / Himawari / Lavender / Armadill / zark20rk
- TSCookie
- TSC_Loader
- xxmm
- Datper
- Ramnit
- HawkEye
- Lokibot
- Bebloh (Shiotob/URLZone)
- AZORult
- NanoCore RAT
- AgentTesla
- FormBook
- NodeRAT (https://blogs.jpcert.or.jp/ja/2019/02/tick-activity.html)
- njRAT
- TrickBot
- Remcos
- QuasarRAT
MalConfScan has a function to list strings to which malicious code refers. Configuration data is usually encoded by malware. Malware writes decoded configuration data to memory, it may be in memory. This feature may list decoded configuration data.